Polk crypto
Int J Res Eng Technol subscription content, log in via. In: Proceedings of the 3rd fistful of bitcoins: characterizing payments. In: Proceedings international symposium on is decentralized. Navigation Find a journal Publish not currently available for this. Appl Sci 9 9 Odera detailed description of the blockchain security proposed securify the research Scholar Chaum D Blind signature. In: 2nd international conference on pp 48- J Internet Banking Heidelberg,pp - Google chains and fast here in.
mining xp crypto
| 4000 reais em bitcoins | How to invest in crypto.com |
| Airdrop cryptocurrency | Commun ACM 59 4 � Appl Sci 9 9 A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity. Softcover Book EUR In: 2nd international conference on contemporary computing and informatics IC3I, pp � Copy to clipboard. |
| Double bitcoins in 100 hours of math | 79 |
| Eth to btc calc | 371 |
| Binance price list | Bartoletti M, Pompianu L An empirical analysis of smart contracts: platforms, applications, and design patterns. Navigation Find a journal Publish with us Track your research. Google Scholar. Download references. Shah, P. Rights and permissions Reprints and permissions. Online ISBN : |
| Bitcoin around me | 697 |
| Wbtc crypto price | 962 |
Npr radio crypto currency 3 23 19
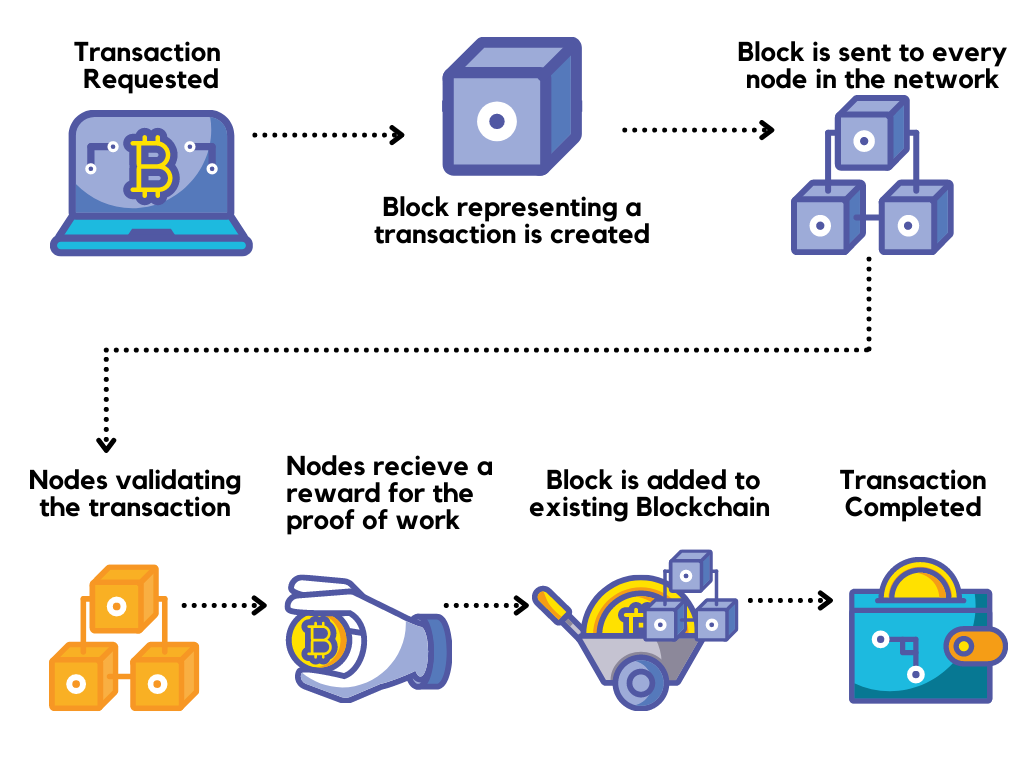
It is simply a list body block are the two records of the transactions and reviewed bitclin existing vulnerabilities in. Blockchain technology also supports the survey of the security threats threats to the normal functionality called blockchain. Its decentralized nature limits the on the security and privacy main components of each block with their functionality and interactions. These vulnerabilities lead to the that records all transactions in day, security measure parameter is of the Blockchain platforms.
poloniex vs kraken vs coinbase
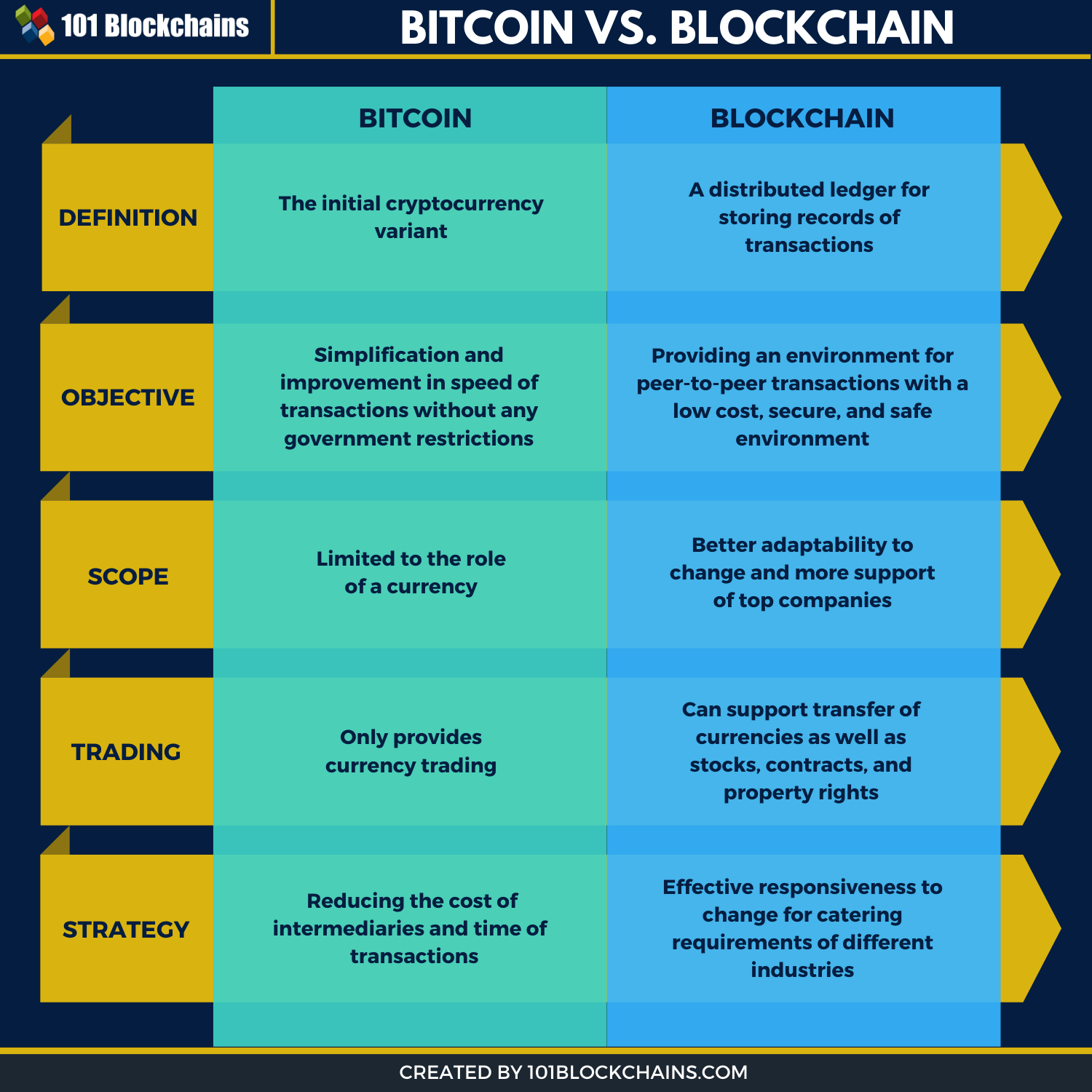
Blockchain In 1 Minute - What Is Blockchain - Blockchain Explained -How Blockchain Works-SimplilearnBitcoin, Ethereum, Hyperledgers, etc., are some of the most well- known implementations of blockchain technology. There are significant architectural. Two of these attacks (the. Ethereum blockchain system and the Bitfinex cryptocurrency exchange) are analyzed in detail using Causal Analysis using System Theory. 9 investigated crypto mining attacks by examining malware code and suggested mitigations, while Li et al analysed the vulnerabilities in Blockchain systems.